Subject Access to OPAC
The typical OPAC interaction process requires the matching or crude translation of user vocabulary to system vocabulary. It became apparent that the amount of subject information included in standard MARC records is not adequate to meet the users' subject approach to the OPAC. Online capabilities offer many possibilities for improved subject access. Two important search devices used in OPACs are discussed below:
Boolean Search
Boolean search is the process of searching where the search terms are combined through Boolean Operators (AND, OR, NOT)
Logical Product AND' Here two or more terms are combined by logical "AND" in order to formulate the search statement. If we formulate the search statement as A and B, we require that matching for both A and B in the index record to take place. Thus, a search for 'Electronic Scanner' seeks to formulate the search statement as 'Electronic AND Scanner'.
Logical Sum 'OR': Here two or more terms are combined by logical 'OR'. Thus, a search for 'Electronic Scanner' or 'Electronic Searcher' seeks to formulate the search statement as 'Electronic AND (Scanner OR Searcher)'.
Logical Difference 'NOT': Here, terms are combined by logical 'NOT'. If we formulate the search statement as A NOT B, we require that, for matching, A must be present in the index, record but B must be absent. Thus a search statement '(Automation AND Library) NOT Circulation' will retrieve all index records concerning 'Library automation' except 'Circulation'.
In this connection, it is to be noted that different OPACs have their own symbols used to indicate the Boolean operators (AND, OR, NOT) while formulating the search statement. The Boolean search method is also explained is BLIS - 06 and BLIS - 07 courses.
Truncation
It is not necessary to specify complete words. The system may allow for 'term truncation', where a fragment can be specified and the computer will pick up any term containing that fragment. This device is also known as 'Word fragment search'. Fragments may be truncated at either or both ends or at the middle. As for example:
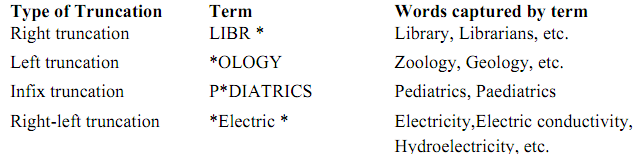
The sign '*' is used to indicate truncation. The sign may vary from one system to another system.