Task: Sets and bags
In mathematics, the notion of multiset (or bag) is a generalisation of the notion of set.
A bag is a special kind of container in which the items may be repetitive, and without any order. A set is a container in which items may NOT be repetitive (each element in a set is unique).
Our purpose in this assignment is to implement the set and bag concept by using an array-based list structure.
The program
This assignment will be implemented by the use of 2 interfaces named:
1. SetList
2. BagList
The SetList interface will contain the following method headers:
Sets
The implementation of the SetListType has to take into account the fact that repeat values are not stored. The only requirement as far as this assignment is concerned, is that you use an array-based list structure to implement both sets and bags.
Bags
The implementation of the BagListType has to take into account the fact that repeat values are stored. For the purposes of this assignment , we will employ a dual array technique so as to eliminate having to physically store a value (object) we have already put into our bag structure. One array will store the object, the second array will store the number of times this object is present in our bag structure (i.e., the second array is of type int)For example, for an input of Integers of the following values:
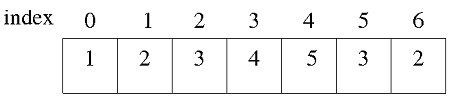
1 2 3 4 5 3 2
These values would normally be stored in a single array as shown below.