Importance of Project Management as it relates to Information Security Program:
Information security means protecting your information and data from unauthorised access, disclosure, modification, use, purging or deletion. Companies have started to realise the importance of information security and are allocating separate budget and human resources for it. It has matured into a separate business enabler function in many organisations. Organisations now face myriad regulatory requirements and the need to manage risk and information theft. Therefore, it is important for organisations to recruit people with specific skills so that information assets are safe and the continued integrity of information is assured. Thus project management methodologies that help in keeping information secure is of great importance for any organisation. (Mariana Gerber, Rossouw von Solms, Paul Overbeek; 2001)
PMBoK for a security program:
Project management book of knowledge (PMBoK) is a set of guidelines for project management and it is considered to be industry's best practices. It is a foolproof method and ensures that no problems are overlooked. There are mainly nine knowledge areas in PMBoK and every managerial function/process falls under it.
1. Project Integration Management: When people inside an organisation do not feel the need for information security, they do not follow policies and procedures made for security. Information security personnel need to motivate people to follow security policies and educate them about its importance and relevance.
2. Project Scope Management: Manager should define the scope and activities required for information security accurately.
3. Project Time Management: It requires project to be completed by the predefined completion date with meeting all of its objectives. Security programs should be planned in such a way that there is optimum time to finish all the security activities.
4. Project Cost Management: Managers and information security personnel should ensure that project gets completed in its allocated budget. It requires managers to estimate for all the resources correctly.
5. Project Quality Management: Security personnel should ensure that work they do meet required quality standards and expectations. For example they should make efficient software to catch information security violations.
6. Project Human Resource Management: Manager should ensure that most eligible, efficient and experienced people are chosen for security programs. They should identify such information security professionals to complete the project.
7. Project Communication Management: Manager should share details and updates required for proper functioning of security project with team members on timely basis.
8. Project Risk Management: Information security projects may face higher risks than other projects so managers should plan well in advance for such an event and have to be ready for contingency plans.
9. Project Procurement Management: It needs different type of software and hardware to perform their task successfully. Employees should be provided with such resources and there should be proper infrastructure for the same. (Lam-for Kwok, Dennis Longley; 1999)
Importance of process and project maturity in security program:
There are five processes involved in project management of information security program. They are initiating, planning, executing, controlling and closing. Process maturity can be defined as how close a process is to being complete or capable of further improvements through timely feedbacks. It evaluates process and project on timely basis and if progress is not acceptable then corrects it. If progress is satisfactory then it is declared to be completed successfully. This procedure is very important because it helps employees to remain focused to a security program.
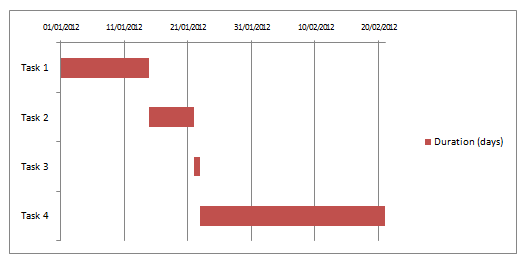
Let's take an example of a company where management wants to implement certain policies and regulations for information theft and its violations. First it is assigned to suitable person for policy and regulations formation. (Task 1: Duration 2 weeks) It is then reviewed by management and changes are done if necessary. (Task 2: Duration 1 week) Then these policy documents and information is broadcasted to all the employees of the company. (Task 3: Duration 1 day) Security personnel then educate employees about the benefits of the policy and possible losses for violation cases. (Task 4: Duration 1 month)