Modular programming denotes to the practice of writing a program as a sequence of independently assembled source files. Every source file is a modular program intended to be assembled in a separate object file. Every object file constitutes a module. The linker collects the modules of a program in a coherent whole.
There are various reasons a programmer may choose to modularise a program.
1. Modular programming allows breaking a large program in a number of smaller modules each one of more manageable size.
2. Modular programming makes possible to link source code written in two separate languages. A hybrid program written partly in assembly language and partly in higher level language necessarily involves at least one module for each language involved.
3. Modular programming enables for creation, maintenance as well as reuse of a library of generally used modules.
4. Modules are easier to grasp.
5. Different modules may be assigned to different programs.
6. Debugging and testing may be done in a more orderly fashion.
7. Document action can be easily understood.
8. Modifications can be localised to a module.
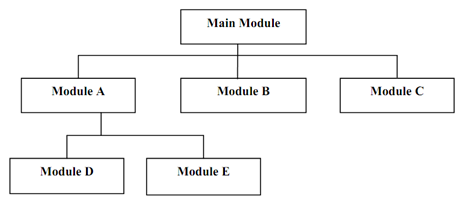
A modular program can be signified using hierarchical diagram:
The main advantages of modular programming are:
1. Easier, smaller modules to manage
2. Code repetition can be avoided by reusing modules.
We can split a program into subroutines or procedures. We need to CALL the procedure whenever needed. A subroutine call handovers the control to subroutine instructions and brings the control back to calling program.