Expertsmind brings you unique solution in java assignments
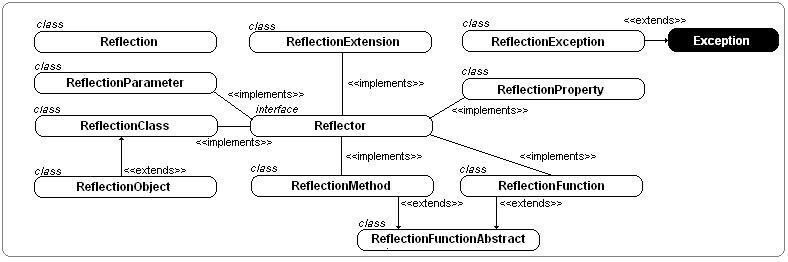
Reflection API
Uses of Reflection with java assignment help
Reflection is widely used by applications which require the capability to analyze or change the playback conduct of applications managing in the Java exclusive device. This is a relatively innovative function and should be used only by designers who have a powerful understanding of the basic principles of the terminology. With that warning in thoughts, expression is a highly effective strategy and can allow applications to execute functions which would otherwise be difficult.
Extensibility Features with java assignment help
A program may create use of exterior, user-defined sessions by developing circumstances of extensibility things using their fully-qualified labels.
Class Surfers and Vision Progression Environments
A category internet visitor needs to be able to enumerate the associates of sessions. Vision development conditions can benefit from making use of type information available in expression to aid the creator in composing appropriate value.
Debuggers and Analyze Tools solutions with java assignment help
Debuggers need to be able to analyze personal associates on sessions. Analyze makes use of can create use of expression to consistently call a discoverable set APIs identified on a category, to guarantee a dangerous of value protection in the test package.
Drawbacks of Reflection
Reflection is highly effective, but should not be used simultaneously. If it is possible to execute a function without using expression, then it is much better prevent using it. The following issues should be kept in thoughts when opening value via expression.
Performance Overhead java assignment help
Because expression includes types that are dynamically settled, certain Java exclusive device optimizations cannot be conducted. Consequently, echoing functions have reduced efficiency than their non-reflective alternatives, and should be prevented in areas of value which are known as frequently in performance-sensitive applications.
Security Restrictions
Reflection needs a playback authorization which may not be present when managing under a protection administrator. This is in an essential factor for value which has to run in a limited protection perspective, such as in an Applet.
Java Exposure of Internals
Since expression allows value to execute functions that would be unlawful in non-reflective value, such as opening personal job areas and techniques, the use of expression can result in unanticipated side-effects, which may provide value alignment and may eliminate mobility. Reflective value smashes abstractions and therefore may change conduct with improvements of the foundation.
Related links :- computer programming assignment help