Input and Output Devices : The most common input devices that you will see in your PC are the keyboard and the mouse.
The keyboard of the computer looks like the keyboard of a typewriter with a few additional keys. One of the most common uses of the computer is as a word processor - basically a sophisticated typewriter that is capable of storing and manipulating text. With a few key strokes the writer can add or delete words and move entire similar sequences or paragraphs from one place to another in the text. Entire books can be written, edited, and printed with the use of computer discs without the manuscript even being committed to paper.
The mouse is a pointing device which is used while working with a display based computer system. It points or selects some area of display on the screen of the monitor and can be moved to another area of the screen. There are several other input devices like scanners, optical pens, joy-sticks that you may see associated with computing systems depending on the kind of requirements.
The output devices of the computer present the results of its work to users. The most common output device is the monitor which looks like a TV screen and the printer.
The input and output devices are so closely related that they are referred to as input/output or 110. The most common I10 devices are floppy discs, compact discs, modem (Modulator-DEModulator) that connect to telephone lines. There are several other devices that can be connected to the computer.
These are called peripherals. I10 peripherals are XY plotters to print graphs, devices that recognise and produce sounds, optical scanners to see text.
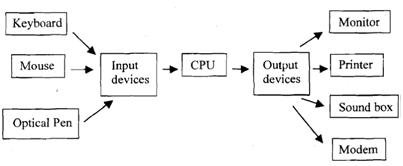
Figure : Components of a Computing System.