Describe language processing activities?
There are two different kinds of language processing activities:
a. Program generation activities
b. Program execution activities
Program generation activities: A program generation activity tends at automatic generation of a program. A specification language is source language of an application domain and the target language is classically a procedure oriented programming language. The given figure below shows program generation activity
program generation activity
The program generator is a software system that accepts the requirement of a program to be generated and makes a program in the target. PL. The program generator initiates a new domain in between the application and PL domains. We call it the program generator domain. The specification gab is here gabbing in between the application domain and the program generator domain. Such gab is smaller than the gab in between the application domain and PL domain.
Program execution activities: A program execution activity classifies system. Two model program executions are:
a. Translation
b. Interpretation
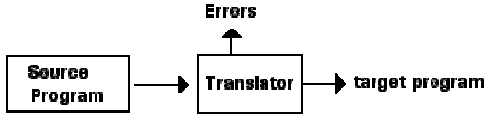
Translation: The program translation models bridges execution gap through translating a program written into a PL, called the source program in an equivalent program in the assembly or machine language of the computer system.
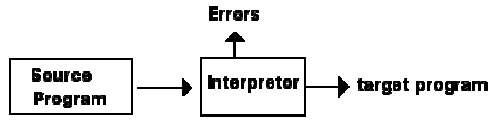
Interpretation: The interpreter reads the source program and stores this in its memory. Throughout interpretation this takes a statement, finds its meaning and performs actions that implement this.