Question:
(a) The following table (table 1.0) gives the length of the CPU burst time in milliseconds of processes P1 to P4. Assume the processes arrived in the order P1, P2, P3, P4 all at time 0.
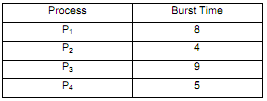
Create a Gantt chart for each of the scheduling algorithms below showing when each process will be scheduled, and also determine the average waiting time for each of them.
I. First-Come-First-Server (FCFS)
II. A non preemptive Shortest Job First (SJF)
(b) Consider table 2.0, below:
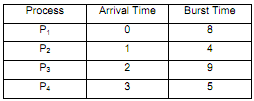
Assume the processes arrived in the order P1, P2, P3, P4 at time shown and need the indicated burst time (both in milliseconds). Create a Gantt chart for the preemptive Shortest Job First (SJF) scheduling algorithm showing when each process will be scheduledand also determine the average waiting time for each process.
(c) Compare the average waiting time from part a (ii) for the nonpreemptive SJF algorithm with the average waiting time in part b for the preemptive version of SJF. Which algorithm results in the minimum average waiting time?
(d) The SJF algorithm tries to reverse the bias against short jobs found in FCFS scheme. Explain how is this achieved and what new problem is then inherent in the SJF algorithm in terms of processes? Is there any way to solve this inherent problem in the SJF algorithm?