Address phase timing:
On the rising edge of clock 0, the initiator notes IRDY # and FRAME# both high, and GNT# low, so it drives the command, address and asserts FRAME# in time for the rising edge of c lock 1. Targets latch the address and start decoding it. They can respond having DEVSEL# in time for clock 2 (fast DEVSEL), 3 (medium) or 4 (slow). Subtractive decode devices, by seeing no other response by clock 4, may respond on clock5. If the master does not observe a response by clock 5, it will dismiss the transaction and remove FRAME# on clock 6.
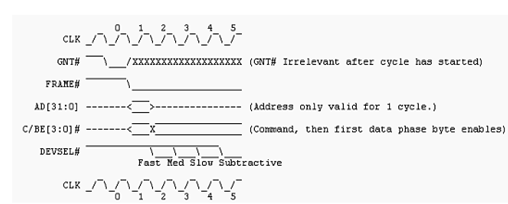
TRDY# and STOP# are deserted (high) during the address phase. The initiator can assert IRDY# as soon as it is prepared to transfer data, which could theoretically beat the time clock 2.
Arbitration:
Any particular device on a PCI bus that is capable of acting as a bus master can initiate a transaction having any other device. To ensure that only 1 transaction is initiated at a time, each master have to wait first for a bus grant signal, GNT#, from an arbiter located on the motherboard. Each device has a distant request line REQ# that requests the bus, but the arbiter may "park" the bus grant signal at any device if there are no present requests. The arbiter can remove GNT# at any particular time. A device which loses GNT# may complete its existing transaction, but may not begin one (by asserting FRAME#) unless it observes GNT# asserted the cycle before it start.
The arbiter can also provide GNT# at any particular time, by including during another master's transaction. At the time of transaction, either FRAME# or IRDY# or both are asserted; when both are deserted, the bus is id le. A device can initiate a transaction at any time that GNT# is asserted and the bus is idle.