A basic model of Database Access Control
Models of database access control have grown out of previous work on protection in operating systems. Let us talk about one simple model with the help of the following example:
Security problem: Consider the relation:
Employee (Empno, Name,Deptno, Address, Salary, Assessment)
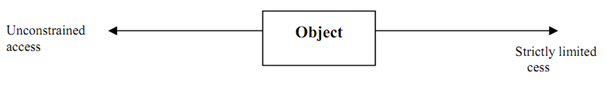
Suppose there are two users: General user and Personnel manager. What access rights may be approved to each user? One extreme possibility is to approve an unconstrained access or to have a limited access.
One of the mainly influential protection models was developed by Lampson and extended by Denning and Graham. This model has 3 components:
1) A set of objects: Where objects are the entities to which access must be controlled.
2) A set of subjects: Where subjects are entities that request access to objects.
3) A set of all access rules: Which can be thought of as forming an access (often referred to as authorisation matrix).
Let us make a sample authorisation matrix for the given relation:
|
Object
Subject
|
Empno
|
Name
|
Address
|
Deptno
|
Salary
|
Assessment
|
|
Personnel
Manager
|
Read
|
All
|
All
|
All
|
All
|
All
|
|
General
User
|
Read
|
Read
|
Read
|
Read
|
Not accessible
|
Not accessible
|
As the over matrix shows, General user and Personnel Manager are the two subjects. Objects of database are Empno, Address, Name, Deptno, Salary and Assessment. As per the access matrix, Personnel Manager can do any operation on the database of an employee except for updating the Empno that might be self-generated and once given cannot be changed. The general user can only read the data but cannot update, insert or delete the data into the database. Also the information about the salary and assessment of the employee is not accessible to the general user.
In summary, it can be said that the basic access matrix is the representation of basic access rules. These rules may be executed using a view on which several access rights may be given to the users.