Reference no: EM131324687
Assignment
1. Many more square-wave digital encoding schemes exist than NRZ-L, NRZI, Manchester, differential Manchester, and bipolar-AMI. List three other encoding techniques and show an example of how each encodes.
2. You have been asked to recommend a type of wiring for a manufacturing building. The size of the building is 200 meters by 600 meters (corresponding to about 650 feet by 2000 feet), and it houses large, heavy machinery. Approximately 50 devices in this building must be connected to a computer system. Each device transmits data at 2 Mbps and sends a small packet of data every two to three seconds. Due to various building-related factors, any cable used for this network has to be suspended high overhead in a hard-to-reach location. What type of cable would you recommend? Use the media selection criteria introduced in the Textbook to elucidate your answer.
3. Consider a VGA screen that has 640 x 800 pixels per screen. Further assume that each pixel is 24 bits (8 for red, 8 for blue, and 8 for green). If a movie video presents 30 frames (images) per second, how many bytes will a two-hour movie require for storage? How many bytes can a standard DVD hold? What then must be the compression ratio?
4. In a sliding window error control system, Station A sends three packets with bytes 0-100, 101- 200, and 201-300, respectively. The second packet with bytes 101-200 is held up somewhere in the network long enough that the third packet arrives before the second one. Create a diagram of this error control scenario and show the response(s) that Station B will send. Now assume that five seconds after Station B responds, the second packet shows up. What does Station B do now?
5. A transparent switch is inserted between two local area networks ABC and XYZ. Network ABC has workstations 1, 2 and 3, and network XYZ has workstations 4, 5, and 6. Show the contents of the two forwarding tables in the switch as the following packets are transmitted. Both forwarding tables start off empty.
• Workstation 2 sends a packet to workstation 3.
• Workstation 2 sends a packet to workstation 5.
• Workstation 1 sends a packet to workstation 2.
• Workstation 2 sends a packet to workstation 3.
• Workstation 2 sends a packet to workstation 6.
• Workstation 6 sends a packet to workstation 3.
• Workstation 5 sends a packet to workstation 4.
• Workstation 2 sends a packet to workstation 1.
• Workstation 1 sends a packet to workstation 3.
• Workstation 1 sends a packet to workstation 5.
• Workstation 5 sends a packet to workstation 4.
• Workstation 4 sends a packet to workstation 5.
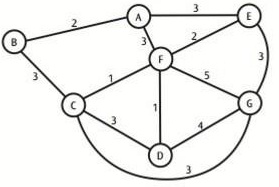
6. Using the procedure for Dijkstra's algorithm and a weighted network graph shown below, find the least-cost route from Node A to all other nodes.
7. What are the advantages and disadvantages of using dynamic IP address assignments?
|
Decide to open an individual retirement account
: You decide to open an individual retirement account (IRA) at your local bank that pays 6%/year/year. At the end of each of the next 40 years, you will deposit $5,000 per year into the account (40 total deposits). 3 years after the last deposit, you w..
|
|
What is the value of lease assets and liabilities
: BUSN 5021 What is the value of lease assets and liabilities reported on the company's balance sheet and Assuming a 5% discount rate, estimate the amount of assets and liabilities that the company avoids reporting by using off-balance-sheet financin..
|
|
Should general medical accept the defense department order
: If sales for the balance of the year are expected to be 50,000 units less because of some lost customers who do not return, should the order be accepted? (Ignore any effects beyond one year.)
|
|
Briefly describe the environment
: Briefly describe the environment (temperature, landscape, food sources, etc.) and describe the organism's role in the environment. Determine which organism your chosen organism would be most closely related to using a phylogenetic tree.
|
|
What are the advantages of using dynamic dynamic ip address
: COM309: What are the advantages and disadvantages of using dynamic IP address assignments? Find the least-cost route from Node A to all other nodes.
|
|
Identify events surrounding the native american
: Identify events surrounding the Native American assimilation efforts, specifically the Dawes Act. Distinguish how opportunities in mining and trade out west impacted values during the Gilded Age or were impacted by values of the Gilded Age
|
|
Diversity of species in such a small area
: Why was there such a diversity of species in such a small area? Could these species have been modified from an ancestral form that arrived on the Galápagos Islands shortly after the islands were formed?
|
|
How were your choices received by the supervisor
: What was the main issue of this week's topic?How were your choices received by the supervisor in the simulation?What was the main lesson that you learned from this exercise?Based on the discussion in class, did other people approach the scenario with..
|
|
How many seats should be protected for full-fare passengers
: Demand for discount tickets is unlimited, while demand for full-fare tickets is evenly distributed between 11 and 30 seats. How many seats should be protected for full-fare passengers and not authorized for release to the discounted $250 segment?
|