Reference no: EM131956545
Task 1: Review Questions
Anwers the following questions on a separate sheet during lectue and submit. Students should perform this task individually.
1. List three approaches to message authentication.
2. What is a message authentication code?
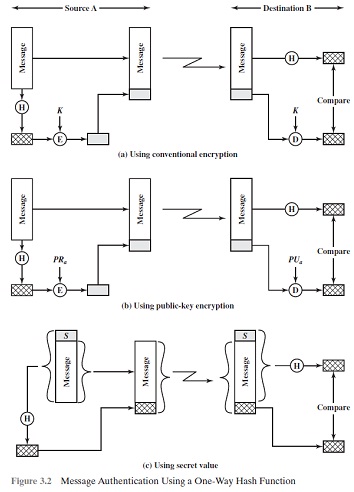
3. Briefly describe the three schemes illustrated in Figure 3.2.
4. What properties must a hash function have to be useful for message authentication?
5. In the context of a hash function, what is a compression function?
6. What are the principal ingredients of a public-key cryptosystem?
7. List and briefly define three uses of a public-key cryptosystem.
8. What is the difference between a private key and a secret key?
9. What is a digital signature?
Task 2: Problems
Anwers the following questions on a separate sheet during lectue and submit.
Students should perform the steps in this task individually.
1. State the value of the padding field in SHA-512 if the length of the message is
a) 1919 bits
b) 1920 bits
c) 1921 bits
2. 3.4 State the value of the length field in SHA-512 if the length of the message is
a) 1919 bits
b) 1920 bits
c) 1921 bits
3. Show the result of encrypting M = 4 using the public key (e; n) = (3; 77) in the RSA cryptosystem.
4. What is the plaintext for the following ciphertext, which was encrypted using a simple substitution cipher: CJBT COZ NPON ZJV FTTK TWRTUYTFGT NJ DTN O XJL. Y COZ ZJV CPJVIK DTN O XJL MYUCN.
Full Alphabet mapping: O = A, L = B, G = C, K = D, T = E, M = F, D = G, P =H, Y = I, X = J, E = K, I = L, B = M, F = N, J = O, R = P, H = Q, U = R, C = S, N= T, V = U, S = V, Q = W, W = X, Z = Y, A = Z.
|
What is bcci cost of equity capital
: The common stock of Buildwell Conservation & Construction Inc. (BCCI) has a beta of .9. The Treasury bill rate is 4%, and the market risk premium is estimated.
|
|
What was the flotation cost as a percentage of funds raised
: The Collins Co. has just gone public. Under a firm commitment agreement, the company received $33.80 for each of the 4.28 million shares sold.
|
|
How much must save at end of each month before retirement
: Collette wants to retire 30 years from now with enough money that she can take out $2, 500 at the beginning of each month for 20 years.
|
|
Calculate the earnings after taxes
: Colter Steel has $5,100,000 in assets. Temporary current assets $ 2,200,000 Permanent current assets 1,560,000 Fixed assets 1,340,000 Total assets $ 5,100,000.
|
|
What are principal ingredients of a public-key cryptosystem
: ITNE - 2002 - Public Key Cryptography and Message Authentication - What is a message authentication code and Briefly describe the three schemes
|
|
What is the beta of blasco books stock
: The common stock of Blasco Books has a standard deviation of 16.4 percent as compared to the market standard deviation of 12.7 percent.
|
|
Calculate amount of interest paid over life of this mortgage
: Calculate your monthly payments on this mortgage. Calculate the amount of interest paid over the life of this mortgage.
|
|
What price does the dividend-discount model predict
: Colgate-Palmolive Company has just paid an annual dividend of $1.23. Analysts are predicting dividends to grow by $0.19 per year over the next five years.
|
|
What is the net present value of investment
: Assume the discount rate is continuously compounded at 8%. What is the Net Present Value of the investment?
|