Reference no: EM13315152
1. Give an example to show that the group of permutations S5 is not commutative.
2. Use ECB mode with block length 3 and the permutation cipher for the following operation:
(a) Encrypt the plaintext 101100101111; key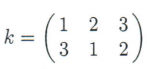
(b) Do the corresponding decryption.
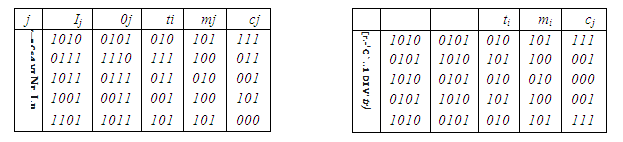
To help with the next two questions, here are examples of block cipher encryption in CFB mode and in OFB mode. In both examples the block cipher, plaintext, and key are the same as in the examples for ECB and CBC modes that were presented in class.
Choose block length r = 3. The plaintext blocks are therefore m1 = 101, m2 = 100, m3 = 010, rn4 = 100, m5 = 101. As initialization vector, use IV = 1010. The CFB encryption is then shown in the left-hand table, and OFB encryption in the right-hand table:
3. Encrypt the plaintext 100101110001 using (a) CFB mode and (b) OFB mode. Use the permutation cipher with block length 3, r = 2, and
key 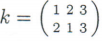 Use initialization vectors 000 in (a) and 010 in (b).
Use initialization vectors 000 in (a) and 010 in (b).
4. Do the decryptions corresponding to 4(a) and 4(b).
5. Use the stream cipher discused in class, with n = 7 and c0 = c1 = 1, c2 = c3 = 0, c4 = c5 = c6 = 1. Encrypt w = 1110011 1110001 1010001 using the key k = 1010011.
6. (Nothing to be handed in). This may be the right time to fa-miliarize yourself with the computer algebra system Maple. See the course website http: //mathstat sdal.cardilcher/4116/ about how to download Maple. Our textbook (Trappe & Washington) has a very nice introduction in Appendix B, with instructions on how to download a special cryptography "notebook" for Maple. Do a few easy examples on the shift cipher and the affine cipher (pp. 498-499). Let me know of any problems you may have.
When we start using Maple in earnest in a few weeks, I will have to assume that everybody is familiar with the system.
|
What is the percent kinetic energy loss
: A projectile with mass .065 kg is fired at and embeds itself in a pendulum with mass .19 kg. What is the percent kinetic energy loss during the perfectly inelastic collision
|
|
Estimate the minimum absolute pressure causing cavitation
: When a fluid flows through a sharp bend, low pressures may develop in localized regions of the bend. Estimate the minimum absolute pressure (pmin in psi) that can develop without causing cavitation if the fluid is water at 80 oF.
|
|
Determine the final density of the gas-carbon dioxide
: Carbon dioxide at 30 C and 320 kPa absolute pressure expands isothermally to an absolute pressure of 170 kPa. Determine the final density of the gas.
|
|
American international automotive industries
: American International Automotive Industries (AIAI) manufactures auto and truck engine, transmission, and chassis parts for manufacturers and repair companies in the United States, South America, Canada, Mexico, Asia and Europe. The company transport..
|
|
Use the stream cipher discused in class
: Use ECB mode with block length 3 and the permutation cipher for the following operation.
|
|
Find the kinetic energy of the system at equilibrium point
: A horizontal block-spring system with the block on a frictionless surface has total mechanical energy E = 55.1 J, What is the kinetic energy of the system at the equilibrium point
|
|
Describe how the speed of sound varies over the range
: An important dimensionless parameter concerned with very high-speed flow is Mach Number, defined as V/c, where V is the speed of the object such as airplane or projectile, and c is the speed of sound in the fluid surrounding the object.
|
|
The ratio of total assets to sales
: McCormac Co. wishes to maintain a growth rate of 6 percent a year, a debt-equity ratio of 0.43, and a dividend payout ratio of 50 percent. The ratio of total assets to sales is constant at 1.34.
|
|
Diabetes and cardiovascular disease
: Explain how NAFLD (Nonalcoholic Fatty Liver Disease) impacts the risk for other chronic diseases, such as diabetes and cardiovascular disease (explain how – it is not adequate to say the risk increases)
|