Reference no: EM133318
QUESTION 1
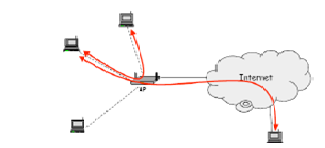
Think about a number of wireless devices (nodes) which are connected to the Internet via a single access point (AP).
a. Provide three reasons why security is more of a concern in this type of wireless network?
(b) Catalogue the three main goals of information security.
(c) Elucidate how CSMA/CA is used with Wireless LANs.
(d) Give details for the differences between war driving and war flying.
(e) Which two forms have favoured adoption of 802.11g over 802.11a?
(f) Portray the diverse steps adopted by an attacker during wireless hacking process.
QUESTION 2
The 802.11 security architecture and protocolis k/n as Wired Equivalent Privacy (WEP) and it is accountable for providing authentication, confidentiality and data integrity in 802.11 networks.
(a) Briefly, describe the differences the flanked by Open System Authentication and Shared Key Authentication, as used in WEP. Which one is more secure?
(b) The absence of any key establishment protocol in WEP led to multiple problems. File any three problems.
(c) Describe the purpose of using beacons while connecting to wireless LANs.
(d) What are the two WEP key lengths?
(e) Elucidate what is meant by the term Initialisation Vector (IV).
(f) WEP has been known to have various security vulnerabilities, leading to its failure.
i. Illustrate any three vulnerabilities of using WEP.
ii. Briefly explicate how FMS attack can be performed and give any one common tool used by attackers.
iii. Though, even today WEP encryption is still used in some networks. Explain how to best make use of WEP in such networks.
QUESTION 3
(a) Provide one reason why WPA2 encryption is preferred over WEP?
(b) By using an appropriate drawing, describe how the 802.1x authentication model is mapped to Wi-Fi.
(c) What do the subsequent acronyms stand for?
i. RADIUS
ii. EAPOL
(d) Give two prominent features of using AES in counter mode for WPA2.
(e) One of the main causes in using EAP is the ability to leverage multiple types of authentication mechanisms. Point out any two such authentication mechanisms.
(f) Regard (notice) the following a list of loopholes found in WEP. Explain how WPA fix each of these loopholes:
i. No protection against replay attacks.
ii. No support for a station to validate a network.
iii. Revealing the master key to attacks like FMS (due to generation of per-packet key)
QUESTION 4
Radio Frequency Identification (RFID) is about devices and technology that use radio signals to swap over the identifying data.
(a) Present two typical uses of RFID systems.
(b) Describe the difference between active and passive tags.
(c) Describe how complacency can cause serious security problems to businesses adopting RFID technology.
(d) Portray two common techniques that fraudsters can adopt in order to temporarily disable RFID tags.
(e) Briefly depict any two types of radio frequency manipulation attacks.
(f) Briefly put in plain words on the following attacks to RFID systems:
i. Relay attack
ii. Side channel attack
(f) Unauthorized tag reading has often been a security challenge for RFID systems. illustrate two mechanisms that can be adopted to enforce confidentiality during transmission of RFID components.
QUESTION 5
(a) Regard (notice) the branch of a Wireless Mesh Network (WMN) where a mobile station MS is within the transmission range of TAP3 and relies on it to get Internet connectivity.
i. Describe the function of a TAP.
ii. Give two benefits of adopting WMNs.
iii. Why is the security of multi-hop routing vital in WMNs
iv. Explain any one technique that an adversary can use to attack the routing mechanism in this scenario.
v. Give two causes why WMNs are not ready for wide-scale deployment.
(b) Vehicular Communications (VC), which is still a research area, is expected to play a central role in the effort to create safer and more efficient driving states after a few decades.
i. Briefly, explain three security vulnerabilities of VC.
ii. Why is privacy an issue in vehicular networks, considering that today's vehicles have license plates?
iii. Network volatility is one of the most significant operational challenges to vehicular communications, thus making security a hard problem. Argue.
(c) Briefly elucidate how the denial of services attacks is performed on mobile nodes by attackers. Also, describe how Mobile IP prevents such denial of service attacks.
QUESTION 6
An overall rise in mobility, coupled with the falling cost of Wi-Fi tools (rigging), has led to a proliferation of Wi-Fi hot spots in public areas, such as coffee shops and airports, to provide Internet accessibility. Though, this proliferation has also engendered growing security concerns.
(a) By the use of a drawing, describe the typical architecture for Wi-Fi hotspots.
(b) List three security vulnerabilities of the controller in Wi-Fi hotspots.
(c) In terms of Wi-Fi hotspot security, explain what a service theft attack is.
(d) Discriminate between active session hijacking and passive session hijacking.
(e) Converse on the defensive security mechanisms that can be employed in order to better secure public Wi-Fi hotspots.
|
Discretionary and mandatory access control
: Logic bombs, War dialing, Ping of death attack, steganography, RSA scheme, digital signature, A chain of certificates, A certificate revocation list, A trust anchor, asymmetric algorithm used by PGP, IPSec mode, IP virtual Private Networks
|
|
Network security
: SLE, ARO, and ALE, behavioural biometric technology, Enterprise Information Security Policy, Issue Specific Security Policy, System Specific Security Policy, firewalls protect network, creating a DMZ during firewall implementation, use of SSL to se..
|
|
Digital forensic investigation
: computer security incident, Trojan Defence, anti-forensics technique, chain of custody, FAT file system, SQLOracleHacks.txt, SQLOracleAttacks.txt, SQLInjection.html
|
|
Computer security incident
: Locard's Exchange Principle, electronic crime scene, modules or DLLs a process, router forensics, Configuration and user, Local logs process and memory, Network Information, File system, Portray the NTP vulnerability of some Cisco IOS routers
|
|
Security vulnerabilities of vc
: single access point (AP), wireless network, CSMA/CA, goals of information security, Wireless LANs, wireless hacking process, Wired Equivalent Privacy (WEP), Open System Authentication and Shared Key Authentication, Initialisation Vector (IV), RADIU..
|
|
Owasp top 10 web application security risks
: Reflected XSS and Stored XSS attack, threat Modeling methodologies, Extended Stack Pointer (ESP) and the Extended Base Pointer (EBP), Canary-based defense to buffer overflow attacks in C language, admin.aspx, Index hijacking, cross-site request fo..
|
|
Cryptosystem
: Block cipher, Primitive root, Confusion, Diffusion, Digital signature, Conventional Symmetric-Key Encryption
|
|
Cyber weapon
: Single Sign On (SSO), Single Sign On (SSO), netstat -an, arp -a, ipconfig /displaydns, MS Config. Means, MS Config. Means, network reconnaissance
|