Reference no: EM131890429
Assignment
You have been hired as part of the networking team at University. After completing orientation and training, your manager calls you into a meeting to discuss your first project.
The university has recently leased a single building in Adelphi, Maryland. The building will house faculty and administrative offices, classrooms, a library, and computer labs. Security is important for UNIVERSITY, as the university must protect students' and employees' data, as well as any intellectual property that University has on its servers and computers. As a result, IT management would like to take the time to review proposals on how best to move forward on security issues. As a junior network engineer, you have been asked to prepare a network proposal on how to set up a secure network infrastructure in the newly leased building to support university operations. The network proposal will require three submissions covering network design, network addressing and security, and network customization and optimization.
After speaking to your manager, you are excited about the project, but you realize you will have a busy schedule. As you are writing your proposal, you will also have to prepare for the CompTIA Network+ Certification exam. One of the conditions of your employment at this university is that you obtain this certification within 60 days of being hired.
The network proposal represents a great opportunity to document your expertise. Additionally, it is also a great opportunity for you to form an integrated view of the different aspects of networking which are tested in the certification exam.
Network Design (i.e., Part 1)
In this section, address each of the following.
A. Define the network topology that will be used and justify the decision.
B. Select the appropriate cables and connectors and justify the decision. Describe where wired connections will be used within or across the two new academic buildings and justify the decision. Students must use both wired and wireless technologies.
o Student should be specific when discussing the models, types, and costs.
C. Select the appropriate networking and internetworking hardware for each building, and justify the decision.
o Student should be specific when discussing the models, types, and costs.
D. Select the appropriate Wide Area Network (WAN) design and wireless configuration, and justify the decision. Students must use both wired and wireless technologies.
o Student should be specific when discussing the models, types, and costs.
E. Consider that faculty, students, and guests can bring their own devices (BYOD) and use their computer in each of the buildings.
o Student should be specific when discussing the models, types, and costs.
F. Select the appropriate computer systems hardware to use to support the faculty, students, and overall network design; and justify the decision(s).
o Student should be specific when discussing the models, types, and costs.
Network Addressing and Security (i.e., Part 2)
In this section, address each of the following.
IP Addressing:
A. Watch How to Subnet a Network Video provided in Content -> Project Instructions
o Review the Network Address Template provided in Content -> Project Instructions -> Project Templates for Parts 1 - 3
o Complete the subnet chart provided at the end of the document.
Security
B. Select each of the firewall types to implement, describe network or host-based placement, and configuration details; and justify each of the decisions.
o Students should be specific when discussing the models, types, and costs.
C. Select an IDS, IPS, or both for the network and justify your decision.
o Students should be specific when discussing the models, types, and costs.
D. Define a DMZ implementation and justify the decision.
E. Select physical security measures for each of the new academic buildings and justify the decision.
o Students should be specific when discussing the models, types, and costs.
F. Select additional network security measures to be implemented and justify the decision. They should include:
o How you will protect against social engineering attacks, and justify your decision.
o How you will protect against faculty or students willingly, or unwillingly introducing malware onto the network, and justify your decision.
o What secure protocols you will require for faculty and students to use while accessing resources internal, or external to the network, and justify your decision.
G. Make explicit that UNIVERSITY will not be liable for any problems arising from personal use of devices in the two buildings.
Network Customization and Optimization (i.e., Part 3)
In this section, address each of the following.
A. Identify network services needed.
B. List additional servers or network devices needed to implement the network.
C. List network security measures to be implemented.
D. Justify the need for the network services, security measures, and devices you've selected.
E. Identify network storage and cloud based services that will be available for faculty and students
o Students should be specific when discussing the configuration and implementation.
F. Identify the proper data protection and backup method and implementation, and justify your decision.
o Students should consider the needs of the administration, faculty, and students.
G. Identify a network monitoring solution and describe how this will enable the optimization of the network, and justify your decision.
o Students should be specific when describing protocol analyzers, network monitoring tools, and packet sniffers
H. Identify how logs will be stored, managed, and how long the university will keep them, and justify your answer
o Students should consider this in the context of the network or cloud based storage selected.
I. Describe the troubleshooting methodology Information Technology (IT) personnel will use when troubleshooting issues across the proposed network implementation.
Building Details
Consider the following building layout:
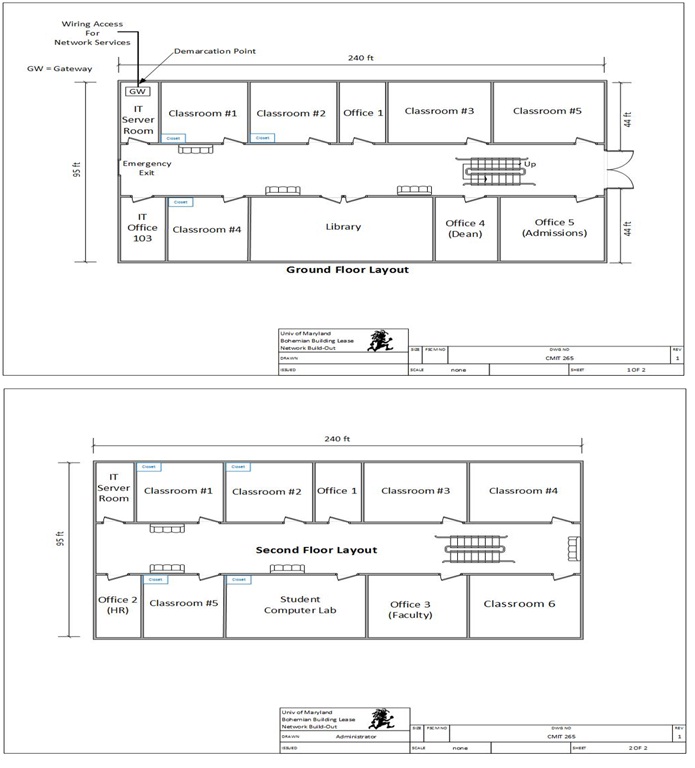
University has not decided how they will use all of the physical space within the newly leased building. However, they have decided to use some of the space. The overall plan is to use the building as provided in the below diagram. However, initially, the building will house five classrooms, one student computer lab, library, and an office.
In the below building diagrams, we will use Office 5 (Admissions) on the first floor. The classrooms are labeled Classroom #1, Classroom #2, and Classroom #4 on the first floor and Classroom #1 and Classroom #5 on the second floor; each computer lab will have a closet. Each lab will have 25 devices: 23 student computers, one instructor computer, and one server in the closet for instructional use. Students should consider high traffic areas for Wi-Fi, such as the sitting areas and not the classrooms. The Wi-Fi network should be segregated from the wired network, and implemented on a separate Class C network. What will the network address, range, and broadcast address for this separate Class C wireless address be?
In addition, there will be a student computer lab that will provide computer access to students to do their homework. There will be 24 computers in this lab and a server in the closet. To allow students access to library resources, the library will also have 10 computers for the general public to use and five computers for library staff.
Finally, there are offices in the building. Each of these offices will have one computer for staff use, with the exception of the admissions office, which will have five computers. There will be two server rooms, one on the first floor and one on the second floor.
Attachment:- Network-Design-Proposal-Template.rar