Reference no: EM133021266
SENG2250 System and Network Security - The University of Newcastle
Aims
This assignment aims to establish a basic familiarity with network security topics via analysing, designing, and implementing solutions.
Questions
1. Network Security
A bank system, including the internal and external sub-systems, is used by different users. Based on the security requirements, these accesses should be protected in different ways depending on access methods. We will focus on network security for internal and external access to the bank system in this task.
• There are two types of users: bank customers and bank employees.
• The bank system provides a range of services, such as personal savings, bank statements, money transfer, internal message management, and account management.
• As a customer, it is allowed to use web browsers to access the bank website and make transactions.
• A customer can also use the mobile app to access the services. In this case, the customer is likely to use a mobile network or WiFi connection.
• As a bank employee, it is allowed to access the bank system via the website or desktop application.
• When an employee is travelling for business, it may need to connect the bank servers via a secure connection.
Your task.
a. Consider the security of the above system, discuss two potential security issues and provide countermeasures.
For each of the issues, specify the related security service(s), attack(s) and mechanism(s). The demonstrated issues must not relate to the same security service(s).
b. Consider that a bank employee requests to modify a bank customer's daily cash transfer limit. Briefly describe the essential security-related step(s) that demonstrate the security checks for the operation. For each step, specify the aimed security service(s).
c. An employee accesses the internal system with proper authentication and authorisation. Consider Kerberos, SAML, and OAuth, which one is better for internal system authentication and authorisation? Justify your answer.
d. To provide secure connection services for the travelling employees, which of IPSec, SSL/TLS, and SSH, would be a better option? Justify your answer.
2. Programming Task
A client and a server are planning to do data exchange. They decide to use a simplified SSL handshake (see Figure 1) to establish a secure channel (session key) then exchange data. The simplified SSL handshake removes the messages for alert, change cipher spec, certificate, etc.
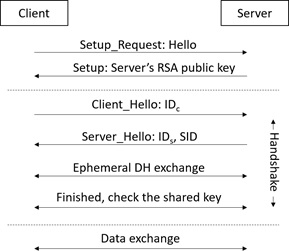
Figure 1. Secure data exchange.
IDC: client ID; IDS: server ID; SID: session ID;
Your task: implement the above mechanism in Java (alternatively C++/Python). The following components are mandatory for implementation.
• Fast modular exponentiation
• RSA signature scheme.
o RSA key generation: randomly generate two primes ??, ?? (for 2048-bit RSA). Set the public key as the fixed ?? = 65537. Server's RSA public key will be sent to the client in the Steup message. Assume this message can be securely delivered, no security protection is needed. Note that a client DOES NOT have its RSA keys.
o RSA signature generation: using SHA256 for message digest computation.
o RSA signature verification: using SHA256 for message digest computation.
o The underlying hash function is SHA256. You can use it from the Java library.
o Key generation needs to be implemented using (Java) BigInteger.
o RSA signature generation and verification need to be implemented using your own fast modular exponentiation method.
• Diffie-Hellman key exchange
o Use the parameters ??, ?? from the System Parameters section.
• The DH key exchange should be secure against man-in-the-middle attacks.
• HMAC
o Use SHA256 as the underlying hash function.
o Use the DH key (e.g., k = g!") to generate the authentication key k′, such that k# = H(k), where H() is the SHA256 hash function.
o HMAC is calculated as (refer to lecture 2)
H(k#, m) = H((k# ⊕ opad)||H((k# ⊕ ipad)||m))
• CTR mode
o Assume a message is always a multiple of 16-byte, i.e. no padding needed.
• Data exchange
o When a shared session key is created, they use 256-bit AES encryption with
CTR and HMAC to protect data confidentiality and integrity, respectively.
o Demonstrate at least two message exchanges, where each message is exactly 64 bytes.
Attachment:- System and Network Security.rar