Reference no: EM133321
QUESTION 1
(a) Explain network security. What are the types of security features used in client server types of network?
(b) What is the disparity sandwiched between authentication and authorization?
(c) What is the most effective biometric authorization technology today? What makes this technology (most) effective?
(d) Give one instance of behavioural biometric technology?
(e) What is a security policy and what are the basic rules when shaping a security policy?
(f) Depict the three types of policy listed below, and give one instance for each type?
- Enterprise Information Security Policy
- Issue Specific Security Policy
- System Specific Security Policy
QUESTION 2
(a) Describe briefly how firewalls protect network? Describe three methods firewall use, to control traffic flowing in and out of a network.
(b) List and briefly describe the 5 stages of a typical intrusion process on a computer network?
(c) What is the point of creating a DMZ during firewall implementation?
(d) Explain the use of SSL to secure a network?
(e) Give one motive why WPA encryption is preferred over WEP?
QUESTION 3
(a) State what you understand by symmetric encryption, public key encryption and hash functions.
(b) State the three deliberations that need to be addressed for encryption to be used effectively in networks?
(c) Illustrate the process of Kerberos Ticket Exchange, using diagram to illustrate your answer?
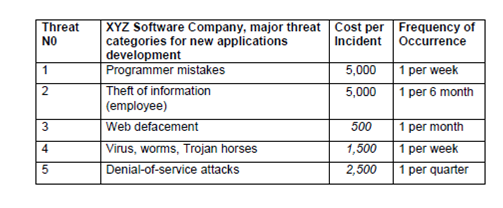
(d) Presume XYZ Software Company is facing a number of information security threats. Using the following table, Compute the SLE, ARO, and ALE for each threat.
|
Define service recovery
: Define service recovery Discuss the impact of the service recovery efforts on customer loyalty
|
|
Turtle shell architecture
: Turtle Shell Architecture, zero-byte representation, Access Control List, DNS Cache Poisoning attack, 16-pass iterative and 9-pass recursive PHP function
|
|
Symmetric encryption algorithms
: block cipher and a stream cipher, Caesar cipher, cryptanalytic attacks, mono alphabetic cipher and a poly alphabetic cipher, Mix Columns, Add Round key, PGP services, traffic padding, contrast link and end-to-end encryption
|
|
Discretionary and mandatory access control
: Logic bombs, War dialing, Ping of death attack, steganography, RSA scheme, digital signature, A chain of certificates, A certificate revocation list, A trust anchor, asymmetric algorithm used by PGP, IPSec mode, IP virtual Private Networks
|
|
Network security
: SLE, ARO, and ALE, behavioural biometric technology, Enterprise Information Security Policy, Issue Specific Security Policy, System Specific Security Policy, firewalls protect network, creating a DMZ during firewall implementation, use of SSL to se..
|
|
Digital forensic investigation
: computer security incident, Trojan Defence, anti-forensics technique, chain of custody, FAT file system, SQLOracleHacks.txt, SQLOracleAttacks.txt, SQLInjection.html
|
|
Computer security incident
: Locard's Exchange Principle, electronic crime scene, modules or DLLs a process, router forensics, Configuration and user, Local logs process and memory, Network Information, File system, Portray the NTP vulnerability of some Cisco IOS routers
|
|
Security vulnerabilities of vc
: single access point (AP), wireless network, CSMA/CA, goals of information security, Wireless LANs, wireless hacking process, Wired Equivalent Privacy (WEP), Open System Authentication and Shared Key Authentication, Initialisation Vector (IV), RADIU..
|
|
Owasp top 10 web application security risks
: Reflected XSS and Stored XSS attack, threat Modeling methodologies, Extended Stack Pointer (ESP) and the Extended Base Pointer (EBP), Canary-based defense to buffer overflow attacks in C language, admin.aspx, Index hijacking, cross-site request fo..
|