Reference no: EM13327693
Scenario: Michelle changes banks following her troubles with FHB. At her new bank, Ultimate Security Trust (UST), she uses RSA as her encryption system. She creates a key pair and supplies to Frank, an officer of UST who will handle her account, with her public key {eA, nA}, securing her private key {dA, nA} on a floppy disk which she keeps locked in a wall safe at her home. In turn, Frank gives Michelle access to a key server maintained by UST so that she can readily obtain his current public key {eF, nF} whenever she needs to communicate securely with him.
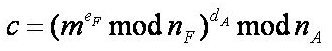
Things are fine for several months until Michelle sends Frank a message m asking about current interest rates on Certificates of Deposit issued by UST. As shown below, she enciphers the message first, and then signs it:
A few days later, Michelle received a statement that shows a debit of $1,000,000 from her account. On inquiring, she was told that Frank transferred the money out of Michelle's account and into an account of his own in a bank on the Caribbean island of Nevis. When reached via long distance in Nevis, Frank produced a message g from Michelle saying: "Thanks for your excellent service, Frank. Please transfer $1,000,000 from my account to yours as a token of my esteem and appreciation. -Signed, Michelle."
Michelle filed suit against Frank, UST and the government of the Nevis, claiming that the message was a forgery sent by Frank himself, and asking for triple damages for pain and suffering. Frank has responded by claiming that all procedures were followed properly and that Michelle is filing a nuisance suit.
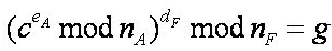
You have been employed by UST as a cryptographic expert to assist in the investigation of this matter. You obtain Frank's private key from the UST server, and the cipher text c, to calculate
Your report to the UST Board of Directors should address the following issues:
• From the facts as presented what can be determined about Michelle's intentions to make Frank a gift of $1,000,000?
• Is there a significance to Caribbean island of Nevis?
• What is the significance of Michelle's message to Frank asking for interest rates?
• Assuming UST wishes to continue using RSA as its cryptographic system, what UST and Michelle could have done to protect against this controversy arising?
Your report not only should clearly address these issues but also response to the reasons the UST board has employed you. You should include, with sufficient detail and background to allow the Board of Directors to understand the issues involved and formulate plans for how to approach the immediate issue with Michelle , and to continue business in the future, assuming that they want to continue using only RSA. Assume that the directors do not know what RSA is and/or how it works.
1. Suppose one of your spy colleagues wanted to send you messages that you could be sure came from him (and not an enemy trying to pretend to be him). Your colleague tells you: "Whenever I send you a message, the last thing in the message will be a number. That number will be a count of the number of letter E's in the message. If you get a message, and the number at the end is NOT an accurate count of the number of letter E's, that message is from an imposter."
a) This number, put at the end of each message, is an example of what cryptographic item?
b) Does it have the characteristic of being one way or can this number be end result of some other rule if so which rule?
c) Is it collision resistant, see b above?
d) Can you suggest some other way to indicate that message is from the sender without encryption?