Reference no: EM132107878
Learning objectives - Apply software tools to troubleshoot common network security problems.
This lab activity requires you to identify and deploy a suitable honeypot to suite the following scenario. An organisation has been the target of recurring network intrusion attempts targeted at their public facing services. To mitigate the risks and better understand the threat, the organisation has decided to deploy honeypots as one of the options.
The following network design (Figure 1) shows three honeypot deployments for the organisation. Your task is to select one honeypot, identify a suitable tool to deploy the honeypot, and provide a detailed guide of how to deploy and customise the honeypot.
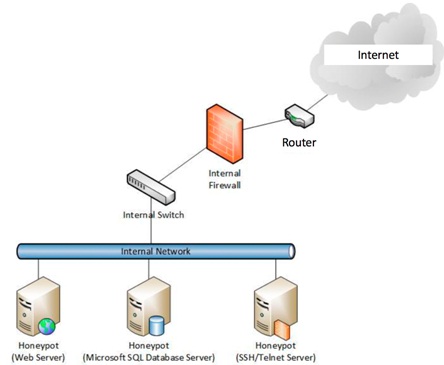
FIGURE 1: HONEYPOT DEPLOYMENT DESIGN
Task
a) Choose a honeypot you want to deploy.
b) Identify a suitable tool to deploy the honeypot you have chosen.
c) Implement the honeypot in a virtual environment (you may use vmware, virtualbox, docker, or any other virtual environment of your choice).
d) Provide a detailed guide for the honeypot deployment with step-by-step instructions. Each step should have screenshots of your implementation as proof.
e) Test the honeypot deployment. This can be done through activity logged or displayed by the honeypot deployed. You will need to show that you have interacted with the honeypot in some way, and that the honeypot has detected or recorded this activity.
f) Provide a technical report proposing your solution, including the following
i. Choice of honeypot
ii. Deployment guide
iii. Test procedure and evidence