Reference no: EM131418509
Technical Project Paper: Information Systems Security
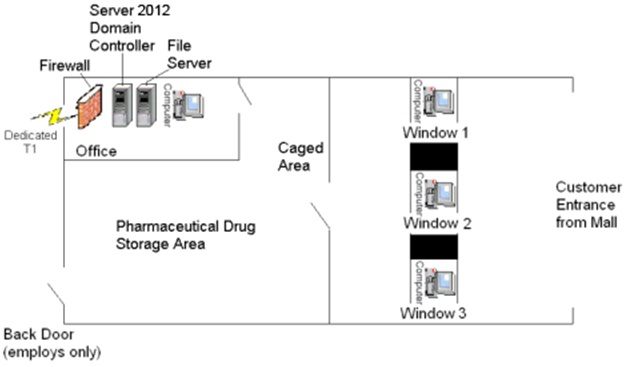
Suppose you are the IT professional in charge of security for a small pharmacy that has recently opened within a shopping mall. The daily operation of a pharmacy is a unique business that requires a combination of both physical and logical access controls geared towards protecting medication and funds located on the premises, as well as the personally identifiable information and protected health information of your customers that resides on your system. Your supervisor has tasked you with identifying inherent risks associated with your pharmacy and establishing strong physical and logical access control methods to mitigate the identified risks.
1) Firewall (1) 4) Desktop computers (4)
2) Windows 2012 Active Directory Domain Controllers (DC) (1) 5) Dedicated T1 Connection (1)
3) File Server (1)
Write an eight to ten page paper in which you:
1. Identify at least five potential physical threats that require attention.
2. Determine the impact of at least five potential logical threats that require attention.
3. Detail the security controls (i.e., administrative, preventative, detective, and corrective) that the pharmacy could implement in order to protect it from the five selected physical threats.
4. Explain in detail the security controls (i.e., administrative, preventative, detective, and corrective) that could be implemented to protect from the five selected logical threats.
5. For each of the five selected physical threats, choose a strategy for addressing the risk (i.e., risk mitigation, risk assignment, risk acceptance, or risk avoidance). Justify your chosen strategies.
6. For each of the five selected logical threats, choose a strategy for handling the risk (i.e., risk mitigation, risk assignment, risk acceptance, or risk avoidance). Justify your chosen strategies.
7. Use at least five quality resources in this assignment (no more than 2-3 years old) from material outside the textbook. Note: Wikipedia and similar Websites do not qualify as quality resources.
Your assignment must follow these formatting requirements:
• Be typed, double spaced, using Times New Roman font (size 12), with one-inch margins on all sides; citations and references must follow APA or school-specific format. Check with your professor for any additional instructions.
• Include a cover page containing the title of the assignment, the student's name, the professor's name, the course title, and the date. The cover page and the reference page are not included in the required assignment page length.
|
Four key best practices in strategic compensation
: Describe three to four key best practices in strategic compensation. Focus on theories or concepts for approaching a total rewards strategy, the significance and impact of job classifications in creating a total rewards strategy and approaches to ..
|
|
Which modifier should be appended to the anesthesia code
: A patient undergoes a pacemaker insertion. She is not expected to survive if she doesn't have the operation. What code should be reported? A patient who has been treated by a physician or another physician in the same group within the last three y..
|
|
Verify that a normal model can be used in given situation
: Psychiatrists estimate that about 1 in 100 adults suffers from bipolar disorder. What's the probability that in a city of 10,000 there are more than 200 people with this condition? Be sure to verify that a Normal model can be used here.
|
|
Thoughts on the following ethical dilemma
: For this week, discuss your thoughts on the following ethical dilemma: You work in HR at a major consulting firm and one of the consultants comes to you and says that he cannot in good faith take an assignment at the Philip Morris company because ..
|
|
Identify potential physical threats that require attention
: Identify at least five potential physical threats that require attention. Determine the impact of at least five potential logical threats that require attention.
|
|
Customer service you feel technically well prepared
: Suppose you have been hired as the new supervisor of a customer service team for a cell phone company. With four years of customer service you feel technically well prepared. However, it is your first formal appointment as a manager. What skills wi l..
|
|
Find mean and standard deviation of the difference in price
: Find the mean and standard deviation of the difference in price of a ticket to China and a ticket to France.- Do you need to make any assumptions in calculating these means? How about the standard deviations?
|
|
Determine enduring leadership
: ADVANCED BRAND MANAGEMENT - Dedication to a brand is vital for sustained brand leadership. Discuss the five (5) factors that determine enduring leadership. Ensure you address all five factors in context of the Levi case study.
|
|
Analyze and synthesize data acquired from integrative case
: The Portfolio Project is due at the end of Module 8. For the Portfolio Project, you will analyze and synthesize data acquired from the Integrative Case, B.R. Richardson Timber Products Corporation (pp. 750-763 of the textbook), and present the find..
|