Reference no: EM131195329
Technical Project Paper: Information Systems Security
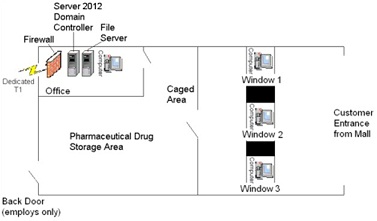
Suppose you are the IT professional in charge of security for a small pharmacy that has recently opened within a shopping mall. The daily operation of a pharmacy is a unique business that requires a combination of both physical and logical access controls geared towards protecting medication and funds located on the premises, as well as the personally identifiable information and protected health information of your customers that resides on your system. Your supervisor has tasked you with identifying inherent risks associated with your pharmacy and establishing strong physical and logical access control methods to mitigate the identified risks.
1) Firewall (1) 4) Desktop computers (4)
2) Windows 2012 Active Directory Domain Controllers (DC) (1) 5) Dedicated T1 Connection (1)
3) File Server (1)
Write an eight to ten page paper in which you:
1. Identify at least five potential physical threats that require attention.
2. Determine the impact of at least five potential logical threats that require attention.
3. Detail the security controls (i.e., administrative, preventative, detective, and corrective) that the pharmacy could implement in order to protect it from the five selected physical threats.
4. Explain in detail the security controls (i.e., administrative, preventative, detective, and corrective) that could be implemented to protect from the five selected logical threats.
5. For each of the five selected physical threats, choose a strategy for addressing the risk (i.e., risk mitigation, risk assignment, risk acceptance, or risk avoidance). Justify your chosen strategies.
6. For each of the five selected logical threats, choose a strategy for handling the risk (i.e., risk mitigation, risk assignment, risk acceptance, or risk avoidance). Justify your chosen strategies.
7. Use at least five quality resources in this assignment (no more than 2-3 years old) from material outside the textbook. Note: Wikipedia and similar Websites do not qualify as quality resources.
Your assignment must follow these formatting requirements:
• Be typed, double spaced, using Times New Roman font (size 12), with one-inch margins on all sides; citations and references must follow APA or school-specific format. Check with your professor for any additional instructions.
• Include a cover page containing the title of the assignment, the student's name, the professor's name, the course title, and the date. The cover page and the reference page are not included in the required assignment page length.
The specific course learning outcomes associated with this assignment are:
• Explain the concepts of information systems security as applied to an IT infrastructure.
• Describe how malicious attacks, threats, and vulnerabilities impact an IT infrastructure.
• Explain the means attackers use to compromise systems and networks, and defenses used by organizations.
• Explain the role of access controls in implementing a security policy.
• Explain how businesses apply cryptography in maintaining information security.
• Analyze the importance of network principles and architecture to security operations.
• Use technology and information resources to research issues in information systems security.
• Write clearly and concisely about network security topics using proper writing mechanics and technical style conventions.
|
What is the probability that this ball is red
: For instance, if a blue ball is picked then it is replaced by a red ball and vice-versa. The process is repeated ten times and then a ball is picked from the box. What is the probability that this ball is red?
|
|
Explain the ntsb party process
: Provides a highly effective and concise overview/introduction; develops a coherent, central theme that is expressed in a well-structured, organized, and logically-consistent manner throughout.
|
|
What are the goals established by the epa and your state
: What is the content of recycled fiber in the paper used by your school/college/ department? What are the goals established by the EPA and your state? (You can find this from the EPA at www.epa.gov.)
|
|
Unused portion of the building for video game rentals
: The World of Videos operates a retail store that rents movie videos. For each of the last 10 years, World of Videos has consistently earned profits exceeding $25,000 per year. the owner was also contemplating using the additional space to rent video ..
|
|
Identify potential physical threats that require attention
: Identify at least five potential physical threats that require attention. Determine the impact of at least five potential logical threats that require attention.
|
|
Find the probability that the three resulting numbers
: A fair die is tossed three times in succession. Find the probability that the three resulting numbers include at least one 3.
|
|
Discuss the trade-off of richness and reach in environment
: Evan and Wurster discuss the trade-off of “richness and reach” in the environment of decreasing costs of information technology and information. How does this trade-off affect business strategies? Please present an example of a transformed business.
|
|
Is polystyrene recycled in your community
: Is polystyrene recycled in your community? If it is not recycled, call the community solid waste/recycling office and ask why it is not. How would you respond to those reasons? If it is, call and ask what happens to it.
|
|
What are the relevant contract law, statutes and law cases
: Prepare a report on Mental Stress And Distress. What are the relevant contract law, statutes and law cases in australia?
|