Reference no: EM131480275
GLOBAL FINANCE, INC. (GFI)
Global Finance, Inc. (GFI) is a financial company that manages thousands of accounts across Canada, the United States, and Mexico. A public company traded on the NYSE, GFI specializes in financial management, loan application approval, wholesale loan processing, and investment of money management for their customers.
GFI employs over 1,600 employees and has been experiencing consistent growth keeping pace with S&P averages (approximately 8%) for nearly six years. A well-honed management strategy built on scaling operational performance through automation and technological innovation has propelled the company into the big leagues; GFI was only recently profiled in Fortune Magazine.
The executive management team of GFI:
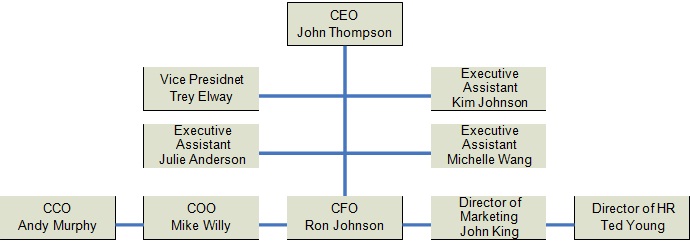
Figure 1 GFI Management Organizational Chart
BACKGROUND AND YOUR GROUPs ROLE
Your Security Company is educated, trained, and hired to protect the physical and operational security of GFI's corporate information system.
Your group was hired by COO Mike Willy and currently report to the COO. You are responsible for a
$5.25m annual budget, a staff of 11, and a sprawling and expansive data center located on the 5th floor of the corporate tower.
CEO John Thompson believes that the IT problem is a known quantity - that is, he feels the IT function can be nearly entirely outsourced at fractions of the cost associated with creating and maintaining an established internal IT department; the CEO's strategy has been to prevent IT from becoming a core competency since so many services can be obtained from 3rd parties. Since the CEO has taken the reigns two years ago, the CEO has made significant headway in cutting the IT department's budget by 30% and reducing half of the staff through outsourcing. This has been a political fight: maintaining and reinforcing the relevance of an internal IT department is a constant struggle. COO Willy's act of hiring you was, in fact, an act of desperation: the increasing operational dependence on technology combined with a diminishing IT footprint gravely concerned Jacobson, and he begged to at least bring in a Company to whom these obligations could be delegated to. Jacobson's worst nightmare is a situation where the Confidentiality, Integrity, and Availability of the information system was compromised - bringing the company to its knees - then having to rely on vendors to pull him out of the mess.
GFI has experienced several cyber-attacks from outsiders over the past a few years. In 2012, the Oracle database server was attacked and its customer database lost its confidentiality, integrity, and availability for several days. Although the company restored the Oracle database server back online, its lost confidentiality damaged the company reputations. GFI ended up paying its customers a large sum of settlement for their loss of data confidentiality. Another security attack was carried out by a malicious virus that infected the entire network for several days. While infected the Oracle and e-mail servers had to be shut down to quarantine these servers. In the meantime, the company lost $1.700, 000 in revenue and intangible customer confidence.
There's no question that the company's CEO sees the strategic importance of technology in executing his business plan, and in this way you share a common basis of principle with him: that IT is a competitive differentiator. However, you believe that diminishing internal IT services risks security and strategic capability, whereas the CEO feels he can acquire that capability immediately and on the cheap through the open market. You're told that CEO Thompson reluctantly agreed to your position if only to pacify COO Willy's concerns.
CORPORATE OFFICE NETWORK TOPOLOGY
You are responsible for a corporate WAN spanning 10 remote facilities and interconnecting those facilities to the central data processing environment. Data is transmitted from a remote site through a VPN appliance situated in the border layer of the routing topology; the remote VPN connects to the internal Oracle database to update the customer data tables. Data transaction from the remote access to the corporate internal databases is not encrypted.
A bulk of the data processing for your company is handled by Oracle database on a high end super computer. The trusted computing based (TCB) internal network is situated in a physically separated subnet. This is where all corporate data processing is completed and internal support team has its own intranet web server, a SUS server, an internal DNS, an Exchange e-mail system, and other support personnel workstations. Each corporate department is segregated physically on a different subnet and shares the corporate data in the TCB network.
OTHER CONSIDERATIONS
1. Ever since the article ran in Fortune about GFI, your network engineers report that they've noted a significant spike in network traffic crossing into the internal networks. They report that they cannot be certain what or who is generating this traffic, but the volume and frequency of traffic is certainly abnormal. The management is very concerned over securing the corporate confidential data and customer information.
2. Increasingly, GFI's CEO Thompson attempts to outsource IT competency. In fact, you've been told of a plan from COO Willy to outsource network management and security functions away from your department and to a service integrator. COO Willy warns you that the political environment will only become more contentious over time; you must make a compelling case as to what value your department can bring over an integrator that can provide secure services at 40% less annual cost than you.
3. The interrelationship between data and operations concerns your company. Increasingly, some of the 10 remote sites have been reporting significant problems with network latency, slow performance, and application time-outs against the Oracle database. The company's business model is driving higher and higher demand for data, but your capability to respond to these problems are drastically limited.
4. Mobility is important for the organization to interact with the customers and other co-workers in near real-time. However, the CEO is concerned with the mobility security and would like to research for the best practice for mobility computing. The CEO is willing to implement a BYOD policy if security can be addressed.
5. Employees enjoy the flexibility of getting access to the corporate network using a WiFi network. However, the CEO is concerns over the security ramifications over the wireless network that is widely open to the company and nearby residents.
6. The company plans to offer its products and services online and requested its IT department to design a Cloud Computing based e-commerce platform. However, the CEO is particularly concerned over the cloud computing security in case the customer database is breached.
ASSIGNMENTS
- Identify and describe the organizational authentication technology and network security issues.
- Make a list of access points internal and external (remote).
- Design a secure authentication technology and network security for GFI.
- Make assumptions for any unknown facts.
- List all known vulnerabilities your group can identify in this environment and address them by proposing a new design. Your group may use any combination of technologies to harden authentication process and network security measures.
- Address the CEO's concern over the mobility security and design a secure mobile computing (smart phones, tablets, laptops, etc.) in terms of authentication technologies and data protection.
- Identify wireless vulnerabilities and recommend what safeguards, authentication technologies, and network security to protect data should be implemented.
- Design a cloud computing environment for the company with a secure means of data protection at rest, in motion and in process.
You are given a fictional scenario above describing security issues affecting organizational assets. You will identify the risks associated with the assets, and recommend mitigating procedures. You will prepare a quantitative / qualitative risk assessment to address risk factors on organizational assets. Your final paper will be 15-25 pages long in a Word document
Evaluate remote access to the networks.
Inventory assets and prioritize them in the order of mission criticality.