Reference no: EM132647368
Assessment: Case Study and Presentation
Introduction
In this assessment you are required to explore the given case study and provide a solution, employing the latest wireless communication techniques. The solution needs to be presented in a report and a short video presentation discussing findings and the proposed solution. The assessment will help in developing an understanding of communication in wireless networks and the limitations and challenges.
Case Study: Home office
Under doctor's orders for more bed rest, Jan received authorization from her employer to work from home during and immediately after her pregnancy. However, to do her job effectively, she routinely needs to retrieve large files from the corporate local area network (LAN), modify them, and return them to another location on the LAN. She also occasionally likes to print something for convenience or record keeping, and she needs convenient access to a telephone. Jan has received instructions from her company's Information Technology (IT) staff regarding how to connect to the corporate LAN.
Jan currently has broadband access to her home. However, the only access is to a PC in a family room in the home's finished basement. Jan's family uses this PC for Internet access, online gaming, and as a resource for school projects. The PC is connected to a colour printer. Jan wants to create a home office in an unused upstairs bedroom. During the later stages of her pregnancy, she wants the convenience of working from more comfortable locations, such as her couch or bed. She already has a cordless phone and is planning to purchase a laptop PC and perhaps a second printer. However, a quick call to her broadband provider has caused her to question the financial feasibility of running new wiring for broadband access in other locations of her home. Perplexed with her problem, Jan talks to some of her co-workers, and one of them mentions wireless. Jan does a little investigation of the wireless LAN products available and decides many of the products are within her budget.
The scope of Jan's solution will be limited by the fact that she already has broadband access installed in her home. She also has instructions for connecting to the corporate LAN. However, she has not checked to see if the wireless home network will affect these instructions. Jan's challenge is that she needs reliable high-speed access to the corporate LAN from the new home office and other convenient locations in the house. She wants to interfere as little as possible with use of the PC in the family room, and she needs her laptop to be inaccessible from the family PC. She would like to have printing capability in the home office. However, her solution must fit within a limited budget. Finally, all equipment that she uses for her solution must be immediately available.
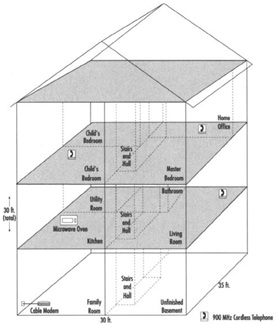
Figure 1. Jan's Site
The proposed solution must consider the following requirements:
• Any locations where she wants to use the laptop should not be more than 100 meters (over 300 feet) away from the access point
• Interference which may be caused by the cordless phone and microwave
• The home network should be cost efficient
• The network needs to be secure
• Other users on the home network
|
Questions about rutherford nuclear model
: What are some unanswered questions about Rutherford's Nuclear Model?
|
|
What is the amount of gain or loss on the disposal
: Un Company sold office equipment with a cost of $39,950 and accumulated depreciation of $35,298 for $6,670. What is the amount of gain or loss on the disposal
|
|
How to calculate the sustainable growth rate
: Calculate the sustainable growth rate. You are given the following information for Clapton Guitars, Inc. Profit margin 6%. Total asset turnover 2
|
|
Determine the number of moles of o atoms
: Determine the number of moles of O atoms in 4.999x10^25 formula units of Mg3(PO4)2
|
|
Employing the latest wireless communication techniques
: Required to explore the given case study and provide a solution, employing the latest wireless communication techniques
|
|
What is the element
: An unknown element reacts with iodine to give the iodide, MI3. If 1.443 g of the unknown element gives 21.804 g of MI3, what is the element?
|
|
Amanda verizon-stages of strategic management
: Select a publicly held company that interests you. Visit the company's corporate website to learn how it engages in strategic management. Remember
|
|
What is the profit margin for easter egg and poultry company
: Easter Egg and Poultry Company has $1,040,000 in assets and $649,000. If the firm has an asset turnover ratio of 4.0 times, what is the profit margin?
|
|
Find the amount of depreciation expense
: If the company uses the units-of-activity method of depreciation, find the amount of depreciation expense for 2018
|