Reference no: EM133074093
CYB5CPR Secure Programming - La Trobe University
Question 1:
Recently you have been hired as a programmer in a cloud-based company. There are ten members in your team. Your team is assigned to build a secure Learning Management System (LMS). The system should have the following requirements.
• User registration (after successful registration with username and password, the program will show a successful message, otherwise it will show a warning message for one failure attempt).
• User login (a user can be a lecturer, student, or administrative staff, who can log in from anywhere).
• Modify learning materials (a lecturer can add and modify learning materials).
• Create discussion (bothlecturer and student can create discussion topics).
• View learning materials (all participants can view learning materials).
In addition to the above-mentioned requirements, you should consider and take care of the security measures such as input validations (e.g., username should not be more than 50 characters, only alphabets and blank space can take as input), buffer overflows, etc. that are relevant to the LMS system.
Now do the following tasks based on the information above.
(a) SECURE REQUIREMENTS. Identify and list the functional requirements and security requirements relevant to this case study.
(b) SECURE DESIGN. List the use cases and misuse cases of the system. Draw a flowchart to illustrate the software design. Reasonable assumptions can be made.
(c) SECURE IMPLEMENTATION. What are the issues do you think you may MOST LIKELY encounter during the implementation (coding) for this case study? Give examples and suggest how to address them. Please discuss at least two issues.
(d) SECURE TESTING. Write the test script to test both the functional and security requirement of the feature "view and answer discussion questions". Reasonable assumptions can be made.
|
Step
|
Action
|
Expected Result
|
|
|
Functional requirements
|
|
|
1
|
User logged in as Student posting a question on discussion form by clicking on Submit.
|
Question should be posted and system should generate message "Question posted successfully".
|
|
2
|
User logged in as Lecturer and clicking on view question
|
Accesses to view the question should be allowed to the user
|
|
3
|
|
|
|
4
|
|
|
|
5
|
|
|
|
6
|
|
|
|
|
|
|
|
|
|
|
Why and what do you think should be performed as part of the secure software testing?
Question 2:
Given the following Python code:
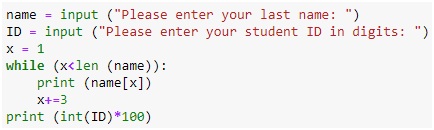
(a) What is the execution outcomeif you enter anything in the "name" and "ID" variables? Please write the justification.
(b) What are the security vulnerabilities in the code based on different input values, and how to address them to make the code more secure? Pleasewrite the secure version of this code.
(c) Why is performance optimization an important aspect of secure software development? Explain with examples.