Reference no: EM131278280
Overview
In this assignment you will develop an event based onetime password (OTP) system. The system consists of the following components:
1. A soft OTP token UI which consists of a push button and a display control. Clicking on the button will generate and display the onetime password.
2. A test UI which will prompt the user to provide the OTP, show access granted message only if the right OTP is entered.
You will need to do the following:
1. Develop, build and test the UI components.
2. Perform Collision Resistance analysis on both algorithms.
Feedback One-Time Password Algorithm (FOTP):
Hash Feedback One-Time Password Algorithm described in the following chart. Secret key is used as the initialization vector. The first OTP is generated by hashing this vector. The second OTP is generated by hashing the hash generated by the first the 1st OTP, and so on. The OTP is calculated by truncating the hash into a six digit value.
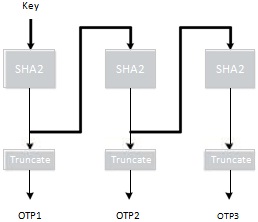
You can set Key = 909670FF00FF00012.
Collision Resistance
This property describes the probability of generating the same OTP over a period of time. A good OTP generation algorithm should demonstrate strong collision resistance. Two metrics are calculated in N number of OTPs:
CR1: the number of similar OTPs in N.
CR2: the number of similar two consecutive OTPs in N.
You will need to submit the following:
1. Complete source code and screen captures of the running program.
2. A study of the collision property. Generate 1,000,000 OTPs using your application. Show a graph describing how the collision properties evolve as the number of OTPs increases.
|
Risk-averse decision-maker and faces a decision involving
: Rose is a risk-averse decision-maker and faces a decision involving the oil rights on a piece of land. A decision analyst helps her determine an appropriate utility function by asking her to consider what she would do in some hypothetical situations.
|
|
Discuss the difficulties managers face
: Discuss the difficulties managers face when expanding globally. Include current examples, that demonstrate corporate failures in balancing profitability with adherence to the law.
|
|
Benefits of the family medical and leave act
: Explain in complete detail the benefits of the Family Medical and Leave Act - date it was passed, it major components and its importance to employees and families
|
|
What codes are applicable-admitted for chemotherapy
: A patient is admitted for chemotherapy (via central vein) for non-Hodgkin lymphoma of the spleen. The patient developed severe nausea and vomiting and was treated for dehydration with IV fluids. What codes are applicable?
|
|
Develop build and test the ui components
: Develop, build and test the UI components - perform Collision Resistance analysis on both algorithms and Generate 1,000,000 OTPs using your application. Show a graph describing how the collision properties evolve as the number of OTPs increases.
|
|
Recently implemented a customer relationship management
: Presume that the organization you selected Walmart has recently implemented a customer relationship management (CRM) system. Research the key elements of a CRM system and defend at least three best practices that your organization can use to improve ..
|
|
Write fifteen user stories for the egrants project organized
: Write 15 user stories for the eGrants project organized by business requirement/epic. The state government currently has a variety of grants management systems across several agencies.
|
|
Channel of distribution to reach consumers
: Many producers use more than one channel of distribution to reach consumers. This may be because they seek to reach different consumers (who shop in different ways or at different stores), or because they wish to reach the same consumer under differe..
|
|
In regression analysis the first thing to be done
: In regression analysis the first thing to be done is
|