Reference no: EM131090698
The overall goal of this lab is to design, implement, and test a peer-to-peer communication system. Peer-to-peer means people on two computers communicate without the people on the other computers seeing the information. The system must use a ring-connected RS232 serial channel (Figure 14.4), must use interrupt-driven I/O, and must have a layered software configuration. The lowest-level software performs serial I/O. The middle-level software sends message packets from one computer to another. The highest-level software interfaces with the human operator (keypad/LCD) and provides a mechanism to create a peer-to-peer connection. In a layered system, software in one layer can call routines only within that layer or the layer immediately below it. You need a way to see who is on the network and a way to request/accept or terminate connection between two operators. Local operator input/output will occur via a keypad and LCD. You may assume all nodes on the system are willing to cooperate and will not perform malicious activity. On the other hand, it is possible that another computer on the network may not be plugged in, or the network connection may be broken
The communication system between two or more microcomputers will be designed in three layers. The first layer, the physical layer is implemented by the SCI hardware and the interrupt-driven device driver. The second layer may consist of a simplified binary synchronous communication protocol (BSC). At this level, message packets will be transmitted between the two machines. Possible formats of the control-code packet and the data packet are shown in Figure 14.25. This control-code packet contains exactly six bytes.
Figure 14.4
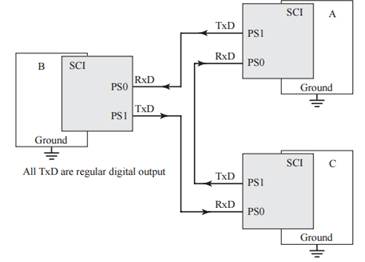
Figure 14.25
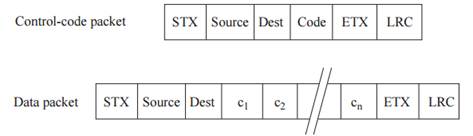
In the data packet, the data c1, c2, . . ., cn are ASCII characters that constitute the information being sent from source to destination. It is OK to limit message sizes to a maximum of 20 bytes. The destination computer will respond with an ACK control packet if the message was received properly and will respond with a NAK if there are any framing, overrun, noise, or LRC errors. The transmitter will send a message and "stop and wait" for either an ACK or a NAK. If an ACK is received, then it can continue. If a NAK is received or if no response is received after a reasonable delay, then the message is retransmitted Because there is a ring physical channel, there is no possibility of a collision. You must handle the situations when the destination computer does not exist or when the ring is broken. To solve this fault you will need some time-out mechanism to retransmit the packet if an ACK is not received in some reasonable time. You should choose an upper limit (e.g., three) on the number of times a packet is retransmitted. After three tries an error is reported to the operator. The highest level will be a keypad interpreter and an LCD display. The LCD should show interactive feedback to the operator creates messages to be sent and should display messages received.
|
Two bible commentaries or religion-centered websites
: Must use at least one or two Bible commentaries or religion-centered websites as well. At the end of your essay you should briefly list the sources that you used, i.e. Arnold and Beyer, Encountering the Old Testament, name/link/date of website, et..
|
|
Explain linux process accounting
: 1. What do you understand about remote logging? 2. Explain Linux process accounting.
|
|
What is required to get this concept developed and tested
: What is required to get this concept developed and tested? Consider timing issues and potential roadblocks.
|
|
Imperative for an organization to learn that strategic moves
: Wrtite a dissertation on given title "It is imperative for an organization to learn that strategic moves should be targeted on the shareholders and that the value should also be delivered to their financial statements"Report should be formed as below..
|
|
Create a peer-to-peer connection
: The LCD should show interactive feedback to the operator creates messages to be sent and should display messages received.
|
|
Determine how comfortable the shopper was in a store
: In a study conducted to investing browsing activity by shoppers, each shopper was initially classified as a nonbrowser, light browser, or heavy browser. For each shopper, the study obtained a measure to determine how comfortable the shopper was in..
|
|
Used to describe such nonstandard instruments
: Suppose that a party wanted to enter into a FRA that expires in 42 days and is basedon 137-day LIBOR. The dealer quotes a rate of 4.75 percent on this FRA. Assume thatat expiration, the 137-day LIBOR is 4 percent and the notional principal is$20,..
|
|
Provide truearth with recommended promotion strategy
: Given your assessment of what this target tribe values and the corresponding product, price, and promotion strategy that you feel TruEarth would have to implement to be successful, do you recommend that TruEarth go ahead with the launch of this li..
|
|
Standard of a harvard business school case
: The aim of the project is to give you an opportunity to apply the concepts learnt in the course to a real life merger/acquisition/divestiture/LBO/restructuring etc. kind of deal.
|