Reference no: EM131148449
Question 1.
We have discussed Prim's algorithm in class for computing the minimum spanning tree (MST). The first step is to codify the network information, i.e., how do we represent the link casts? One way is to use a matrix representation. If the link casts have been expressed as a matrix C, then the (i, j)th element of the matrix gives the cost of the link between i and j (obviously, if i = j, Cii = 0, for all i). For example, the cost matrix for the network shown in Fig. 1 is (first row/column is for node A, second row/column is for node B, etc.):
C =
| 0 |
1 |
5 |
2 |
∞ |
∞ |
| 1 |
0 |
2 |
6 |
∞ |
∞ |
| 5 |
2 |
0 |
1 |
3 |
∞ |
| 2 |
6 |
1 |
0 |
∞ |
4 |
| ∞ |
∞ |
3 |
∞ |
0 |
1 |
| ∞ |
∞ |
∞ |
4 |
1 |
0 |
You can assume that the user would not make any error in entering the link cost matrix (i.e., the matrix would be symmetric, non-negative, and all elements along the leading diagonal will be 0). That is, your code does not need to check for potential errors in the link cost matrix.
Write a function `computePrimMST(sourceID,C)' which takes as inputs the source node ID and the link cost matrix and returns the MST. The pseudocode is available on slide-101 of Chapter-5 notes. The function should return the MST as a 3-column list. The first two columns define the edge chosen and the third column lists the cost of that edge. For example, for the network in Fig. 1, the MST returned by the function could be:
| 1 |
2 |
1 |
| 2 |
3 |
2 |
| 3 |
4 |
1 |
| 3 |
5 |
3 |
| 5 |
6 |
1 |
This means that the edges chosen are (from top to bottom): (i) (A, B) with a cost of 1, (ii) (B, C) with a cost of 2, (iii) (C, D) with a cost of 1, (iv) (C, E) with a cost of 1, and (v) (E, F) with a cost of 1. The total cost of the MST is therefore 8.
You cannot use built in functions which directly compute the MST or im¬plement Prim's algorithm.
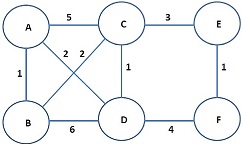
Figure 1: Network for Problem 1.
|
Describe sociocultural values beliefs and practices
: To discuss this, use your own personal experiences, those of someone close to you, or the module material. Describe sociocultural values, beliefs, practices, and/or contexts that can either be helpful or make it more challenging to define one's ow..
|
|
Describe at least three works of early chinese art
: Describe at least three works of early Chinese art; how do these pieces reflect Chinese culture and values? Where did Indian culture originate? In what ways did invaders influence this culture?
|
|
Write an essay in theology
: Write essay in Theology- Foundational to the Christian faith is the belief that mankind is created in the image of God.
|
|
Inter-ocean transfer be responsible under general average
: An Inter-Ocean Transfer cargo ship was forced to jettison some cargo in heavy seas. The various interests in the voyage at the time the property was jettisoned wereValue of the ship: $2.0 millionValue of lumber and wood chips: $1.0 millionValue of ir..
|
|
Compute the mst or implement prims algorithm
: You cannot use built in functions which directly compute the MST or implement Prim's algorithm - You can assume that the user would not make any error in entering the link cost matrix.
|
|
Inter-ocean transfer be responsible under general average
: An Inter-Ocean Transfer cargo ship was forced to jettison some cargo in heavy seas. The various interests in the voyage at the time the property was jettisoned wereValue of the ship: $2.0 millionValue of lumber and wood chips: $1.0 millionValue of ir..
|
|
What modifier should be added to 2nd electrolyte panel code
: A patient is seen in the Emergency Room for dehydration. Diagnostic lab tests are done, including an Electrolyte panel. Before the patient is discharged, the Electrolyte panel is repeated. What modifier should be added to the 2nd Electrolyte panel..
|
|
The ethics of requiring that students subsidize a plagiarism
: The Ethics of Requiring That Students Subsidize a Plagiarism-Detection Service- As you know, the chief responsibility of all educators at the university is to ensure that students receive the best education possible.
|
|
Write an essay that discussing the laborer unrest in america
: Write a 1 and 1/2 page essay discussing the laborer unrest in America from 1877 to the 1970s. Discuss the acts, congress, organizations, and conflicts and consequences.
|