Reference no: EM13185977
1. Give an example to show that the group of permutations S5 is not commutative.
2. Use ECB mode with block length 3 and the permutation cipher for the following operation:
(a) Encrypt the plaintext 101100101111; key k = 
(b) Do the corresponding decryption.
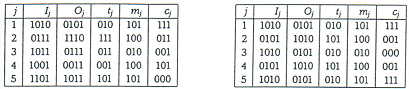
To help with the next two questions, here are examples of block cipher encryption in CFB mode and in OFB mode. In both examples the block cipher, plaintext, and key are the same as in the examples for ECB and CBC modes that were presented in class.
Choose block length r = 3. The plaintext blocks are therefore m1 = 101, m2 = 100, m3 = 010, rn4 = 100, m5 = 101. As initialization vector, use IV = 1010. The CFB encryption is then shown in the left-hand table, and OFB encryption in the right-hand table:
3. Encrypt the plaintext 100101110001 using (a) CFB mode and (b) OFB mode. Use the permutation cipher with block length 3, r = 2, and
key k =  . Use initialization vectors 000 in (a) and 010 in (b).
. Use initialization vectors 000 in (a) and 010 in (b).
4. Do the decryptions corresponding to 4(a) and 4(b).
5. Use the stream cipher discused in class, with n = 7 and c0 = c1 = 1, c2 = c3 = 0, c4 = c5 = c6 = 1. Encrypt w = 1110011 1110001 1010001 using the key k = 1010011.
6. (Nothing to be handed in). This may be the right time to familiarize yourself with the computer algebra system Maple. About how to download Maple. Our textbook (Trappe & Washington) has a very nice introduction in Appendix B, with instructions on how to download a special cryptography "notebook" for Maple. Do a few easy examples on the shift cipher and the affine cipher (pp. 498-499). Let me know of any problems you may have.
When we start using Maple in earnest in a few weeks, I will have to assume that everybody is familiar with the system.
|
What are the expected winnings far a ticket buyer
: what are the expected winnings far a ticket buyer? Express to at least three decimal place accuracy in dollar form (as opposed to cents).
|
|
How to increase sales taxes to bring in badly needed revenue
: Governor Brown, from the state of Taxafornia, wants to increase sales taxes to bring in badly needed revenue to support state operations. He is looking at taxing various goods and services. Will the state tax revenue be great..
|
|
Compute the ionization energy
: Using the thermodynamic data below, and a value of -717 kJ/mol for the Ulattice enthalpy for KCl, calculate the ionization energy of K. Hint: Remember to plug in numbers to the equation given in course content.
|
|
State acetyl serine is completely hydrolyzed
: A reaction mixture containing 20 mM O-acetyl serine, 50 mM NaCl, 50 mM HEPES buffer (pH 7.6), and O-acetyl serine acetylase is incubated in 37C until O-acetyl serine is completely hydrolyzed.
|
|
Commutative and ecb mode
: Give an example to show that the group of permutations S5 is not commutative and ECB mode with block length 3 and the permutation cipher for the given operation
|
|
What are some of the impediments to hiring
: We are in the midst of a slow growing economy in the aftermath of a severe recession. During the economic downturn many businesses laid off workers very quickly once they forecast their sales were dropping. What is the economic reasons behind cutt..
|
|
The absorption of other waste gas components into the water
: Neglect the absorption of other waste gas components into the water, and the evaporation of water into the waste gas stream. What rate is NH3 is being removed from the feed gas? mol/hr
|
|
What is the pressure if the temperature of the system raised
: liquid water and sealed at 25C and a pressure of 1.00 bar. What is the pressure if the temperature of the system is raised to 60.0C?
|
|
Explain problems of adverse selection in rural credit market
: Suppose instead that you (the lender) have no information on the type of borrower and you have to charge a single interest rate to all borrowers. Also assume that the probability that you will end up with each type of borrower is equal (e.g. 1/3 ..
|