Reference no: EM132124035
Advanced Network Design Assessment - Human factors in network analysis and design
Purpose of the assessment - This assignment is designed to assess students' knowledge and skills related to the following learning outcomes:
- Apply concepts and theories of human factors as related to network design and implementation;
- Evaluate performance metrics and dimensions according to specifications.
Assignment Description - In order to design a network, the first step is to collect network requirements. The network requirements are gathered from users and business requirements. The users form one of the important aspects of a successful network design. Your project is to design a network for a sports complex.
Part I: Develop a questionnaire to gather requirements from users, sports complex management, and staff. What kinds of questions would you ask to better understand their environment and each group of users?
Hint [Questions must also be aimed at identifying what applications, the users intend to use.]
Categorise applications identified by users and devise an assessment plan of the applications for network performance.
Part II: Design a network as shown below in Figure 1, and perform a performance test for each set of applications as shown in following Table 1 to validate them. For the network design in Figure 1, Application Sets 1, 2, 3 and 4 in table 1, are located in LAN A, B, C and D respectively.
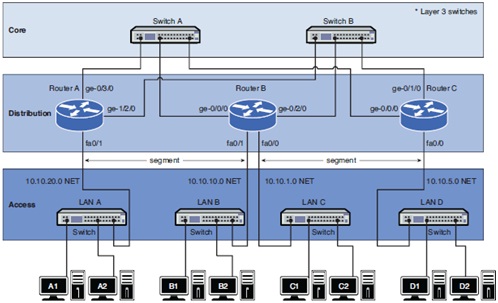
Table 1: Application Performance Requirements
|
Application Set
|
Performance Requirements
|
|
Capacity
|
Reliability
|
Delay
|
|
Application Set 1:
|
|
|
Application 1
|
550 Kb/s
|
N/A
|
N/A
|
|
Application 2
|
700 Kb/s
|
N/A
|
N/A
|
|
Application 3
|
110 Kb/s
|
N/A
|
N/A
|
|
Application 4
|
220 Kb/s
|
N/A
|
N/A
|
|
Application Set 2:
|
|
|
Application 1
|
125 Kb/s
|
99.999%
|
N/A
|
|
Application 2
|
350 Kb/s
|
N/A
|
80ms
|
|
Application 3
|
550 Kb/s
|
99.999%
|
N/A
|
|
Application 4
|
400 Kb/s
|
N/A
|
N/A
|
|
Application Set 3:
|
|
|
Application 1
|
2.1 Mb/s
|
99.95%
|
30 ms
|
|
Application 2
|
1 Mb/s
|
N/A
|
N/A
|
|
Application 3
|
1.1 Mb/s
|
N/A
|
100 ms
|
|
Application 4
|
320 Kb/s
|
N/A
|
N/A
|
Demonstration: Students can demonstrate in a group of 2. Students should be ready with all setup and configurations before the start of the laboratory class. The tutor will ask 2-3 questions of each student to demonstrate any configuration of the setup. The demonstration from each student should not be more than 3 minutes in duration.